CI/CD Pipeline Hardening: Securing GitHub Actions & GitLab CI/CD
Comprehensive guide to building secure and hardened CI/CD pipelines using GitHub Actions and GitLab CI/CD for DevSecOps teams.
by Dan.C
Imagine you’re building a banking app. You’ve encrypted passwords, secured the database, and applied patches. But have you really thought like an attacker? What if someone tries to spoof a user, escalate privileges, or exploit an overlooked vulnerability?
That’s where threat modeling frameworks come in. They give security teams structured ways to anticipate, prioritize, and mitigate threats—long before attackers exploit them. In this guide, we’ll explore the most widely used frameworks: STRIDE, MITRE ATT&CK, PASTA, CVSS, and TMaaC.
Threat modeling is a structured process for identifying what can go wrong in a system and how to defend against it.
Think of it like architecture: when designing a building, architects consider earthquakes, fire hazards, and break-ins. In cybersecurity, we consider spoofing, denial of service, and privilege escalation.
Different frameworks provide different perspectives: some focus on attacker behavior, some on risk scoring, and some on automation.
| Framework | Goal | Strength | Best For | Example Use Case |
|---|---|---|---|---|
| STRIDE | Identify threat categories | Simple, systematic | Developers | Designing a login system |
| MITRE ATT&CK | Map attacker behaviors | Real-world focus | SOC/Blue Teams | Phishing detection |
| PASTA | Risk-based simulation | Business alignment | Enterprises | E-commerce site analysis |
| CVSS | Score vulnerabilities | Global standard | Security managers | Patch prioritization |
| TMaaC | Automate threat modeling | DevSecOps-friendly | Agile teams | CI/CD threat integration |
No single framework solves everything. Instead, they complement each other:
Together, these frameworks form a toolbox for thinking like an attacker, defending like a pro, and scaling security across teams.
Back to our banking app—would you start with STRIDE to identify possible threats, or rely on MITRE ATT&CK to map out attacker behaviors?
The right answer depends on context. The important thing is knowing that frameworks exist to guide you through the complexity of cybersecurity.
If you’re new, start small with STRIDE or CVSS. As your security practice matures, explore MITRE ATT&CK, PASTA, and TMaaC.
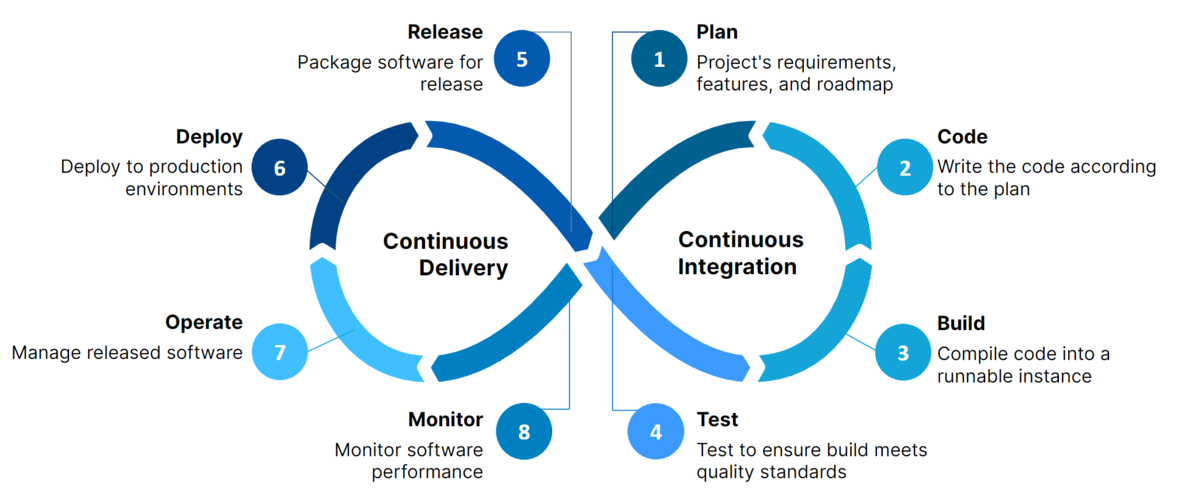
Comprehensive guide to building secure and hardened CI/CD pipelines using GitHub Actions and GitLab CI/CD for DevSecOps teams.
The earlier you model threats, the stronger your defenses will be. — Dan.C
tags: threat-modeling - STRIDE - MITRE - PASTA - CVSS - TMaaC - security