AI Security: Hardening Open-Source and Cloud ML Pipelines
Comprehensive guide to understanding, securing, and hardening AI/ML pipelines in both open-source and cloud environments for security engineers.
by Dan.C
Modern infrastructure (whether cloud-based, on-prem, or hybrid) is dynamic. Configuration changes happen constantly: developers update services, engineers tweak network rules, or automated scripts adjust system settings. While these changes are often intentional, they might introduce configuration drift - a divergence between the desired state defined in your code or policy and the actual state of your infrastructure.
For security engineers, configuration drift is not just an operational concern — it’s a critical security risk. Config drifts may lead to:
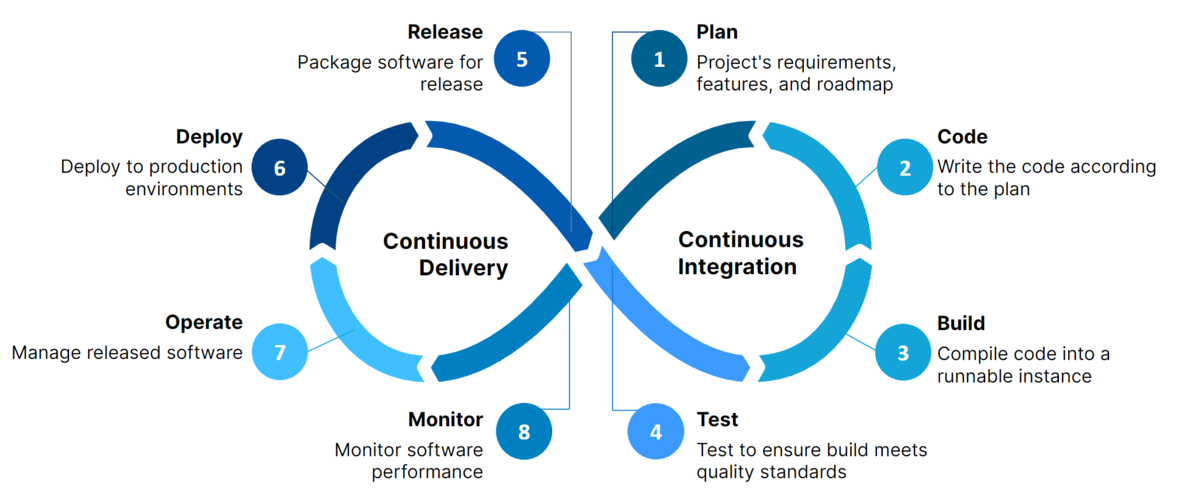
Manual detection of drift across multiple environments is time-consuming and error-prone. Automated auditing scripts and CI/CD integrations are essential to detect, report, and remediate drift quickly, maintaining security, compliance, and operational consistency.
In this post, I’ll explore:
By reading this post till the end, you can have a structured approach to “drift no more”, ensuring infrastructure stays aligned with policy and security expectations.
Configuration drift happens when the real setup of your systems slowly changes from what you originally planned or approved. Even small changes—an extra security group rule, a new IAM permission, a disabled logging setting—can push your environment away from its secure baseline.
Drift usually appears because of:
When drift builds up, you lose control and visibility. Systems that were once secure can become exposed, misconfigured, or non-compliant without anyone noticing.
This is why drift is a real security risk: attackers often exploit misconfigurations that teams did not know existed. Detecting and fixing drift early keeps your environment aligned with the security rules you intended.
Configuration drift is not only an operational problem. It is also a security risk. When systems slowly change from their approved state, they can become easier to attack.
Unexpected open ports or services
A server may start running something that was not part of the plan. Attackers may use it.
Changed permissions
Users or processes may get more access than they should, creating privilege-escalation paths.
Disabled security controls
Logging, firewall rules, or monitoring agents may be turned off without anyone noticing.
Unpatched or inconsistent versions
Some machines may miss updates. Attackers look for these weak points.
Harder investigations
If every machine is different, it becomes harder to understand alerts or reproduce incidents.
Drift detection helps keep systems predictable, hardened, and safe.
Automated auditing is the process of continuously checking systems, configurations, and infrastructure against a known-good baseline. The goal is to detect drift early, reduce manual work, and keep environments consistent and secure.
Baseline Definition
A baseline is the approved configuration. It can be a Terraform state file, an Ansible playbook, a Kubernetes manifest, or a simple JSON/YAML policy file.
State Comparison
The collected state is compared with the baseline.
Differences indicate drift.
Policy Enforcement
Some auditing systems use policies (like OPA or AWS Config Rules) to define what is allowed and what is not.
Continuous Monitoring
Automated audits run on a schedule (every X minutes/hours) or event-driven (e.g., on deployment).
Alerting and Reporting
When drift is found, the system sends alerts through Slack, email, SIEM, or ticketing systems.
Automated auditing creates a feedback loop that keeps infrastructure consistent, compliant, and secure.
Selecting the right tools is crucial for effective drift detection and automated auditing. Tools should help you compare the current state of your infrastructure or configurations against the desired state, provide clear reporting, and ideally allow for remediation.
Several open-source tools are widely used in the security and DevOps community:
Terraform + terraform plan
Detects differences between deployed infrastructure and Terraform configuration.
Can be integrated into CI/CD pipelines for automated checks.
Example:
terraform init
terraform plan -out=plan.out
terraform show -json plan.out
InSpec (by Chef)
Allows writing tests for infrastructure configurations in a human-readable way.
Can check servers, cloud resources, and more.
Example:
describe aws_s3_bucket('my-bucket') do
it { should exist }
it { should_not be_public }
end
Ansible + ansible-playbook --check
Simulates configuration changes without applying them.
Useful for detecting drift in server or application configurations.
Example:
ansible-playbook playbook.yml --check
Cloud providers offer native services for configuration monitoring:
AWS Config
Continuously monitors AWS resource configurations.
Allows defining rules to detect non-compliant resources.
Example: Detect S3 buckets without encryption.
{
"ConfigRuleName": "s3-bucket-encrypted",
"Source": {
"Owner": "AWS",
"SourceIdentifier": "S3_BUCKET_SERVER_SIDE_ENCRYPTION_ENABLED"
}
}
AWS CloudTrail + CloudWatch
Tracks API activity and changes across AWS services.
Enables alerting when configuration drift occurs.
AWS Systems Manager Compliance
Checks managed instances against a desired state defined by State Manager documents.
Using the right combination of open-source and cloud-native tools ensures you can detect drift across both on-prem and cloud environments, providing full coverage for security engineers.
Automated scripts allow security engineers to continuously monitor infrastructure and configuration drift without manual intervention. The goal is to detect deviations from the desired state and optionally trigger remediation or alerts.
Key principles for effective scripts:
Python is popular for writing drift detection scripts due to its rich ecosystem and cloud SDKs.
## drift_check.py
import boto3
## Initialize AWS S3 client
s3 = boto3.client('s3')
## Desired state: All buckets must have server-side encryption enabled
desired_state = True
## Fetch all S3 buckets
buckets = s3.list_buckets()['Buckets']
for bucket in buckets:
bucket_name = bucket['Name']
try:
enc = s3.get_bucket_encryption(Bucket=bucket_name)
status = True
except s3.exceptions.ClientError:
status = False
if status != desired_state:
print(f"DRIFT DETECTED: Bucket '{bucket_name}' encryption is not enabled!")
Explanation:
For quick audits or integration into CI/CD, shell scripts can be useful:
#!/bin/bash
## Desired: All Docker containers running specific version
DESIRED_IMAGE="nginx:1.25"
for container in $(docker ps --format ''); do
image=$(docker inspect --format='' $container)
if [ "$image" != "$DESIRED_IMAGE" ]; then
echo "DRIFT DETECTED:"
echo "Container $container"
echo "running $image instead of $DESIRED_IMAGE"
echo "---"
fi
done
Explanation:
By creating Python or shell scripts with clear logic and logging, security engineers can detect drift early, before it becomes a vulnerability or compliance issue.
Once drift is detected, the next step is bringing your infrastructure back to the desired state. Key strategies include:
Tip: Always log detected drift and applied fixes. This provides auditability and helps identify recurring issues.
Integrating drift detection into your CI/CD pipelines ensures that infrastructure stays consistent automatically. Key points:
Example: A GitHub Actions job can run a Terraform plan and compare it to the applied state to detect drift before merging changes.
Effective drift detection isn’t just about running scripts—it’s about knowing when something goes wrong and taking action quickly.
Key points:
Preventing drift is always easier than fixing it. Security engineers should follow these key practices:
Following these practices helps minimize surprises, maintain security posture, and reduce operational risks.
Configuration drift is a hidden risk that can silently undermine security and stability. By implementing automated drift detection, integrating checks into CI/CD pipelines, and following best practices for prevention, security engineers can:
“Drift No More” is not just a goal—it’s a continuous practice that keeps your infrastructure secure, consistent, and reliable.

Comprehensive guide to understanding, securing, and hardening AI/ML pipelines in both open-source and cloud environments for security engineers.
Comprehensive guide to building secure and hardened CI/CD pipelines using GitHub Actions and GitLab CI/CD for DevSecOps teams.

Hands-on guide for engineers to implement secure GitHub organizational access & secrets management at scale.

Learn Terraform from scratch with this beginner-friendly guide. Step through setup, key concepts, and practical examples—plus grab the ultimate command...
A focused guide on securing Terraform infrastructure-as-code, covering state file protection, least privilege, secrets management, and guardrail automation
Drift detection is not optional—it’s a cornerstone of modern security engineering. — Dan.C
tags: configuration-drift - auditing - automation - devsecops - security-engineering - compliance - infrastructure-as-code - monitoring