AiTM Phishing Bypass MFA
A technical overview of Evilginx, how it works, why attackers use it to bypass MFA, and how defenders can detect...
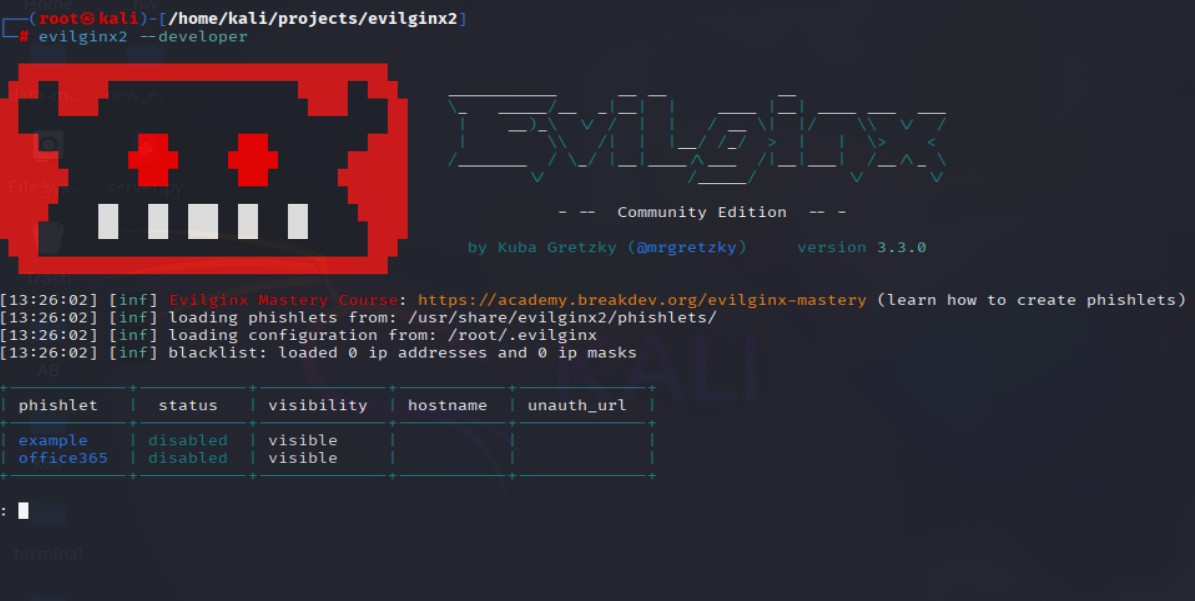
A technical overview of Evilginx, how it works, why attackers use it to bypass MFA, and how defenders can detect...
Practical guide for security engineers to automate auditing scripts that detect and remediate configuration drift in cloud and on-prem environments....

Comprehensive guide to understanding, securing, and hardening AI/ML pipelines in both open-source and cloud environments for security engineers.
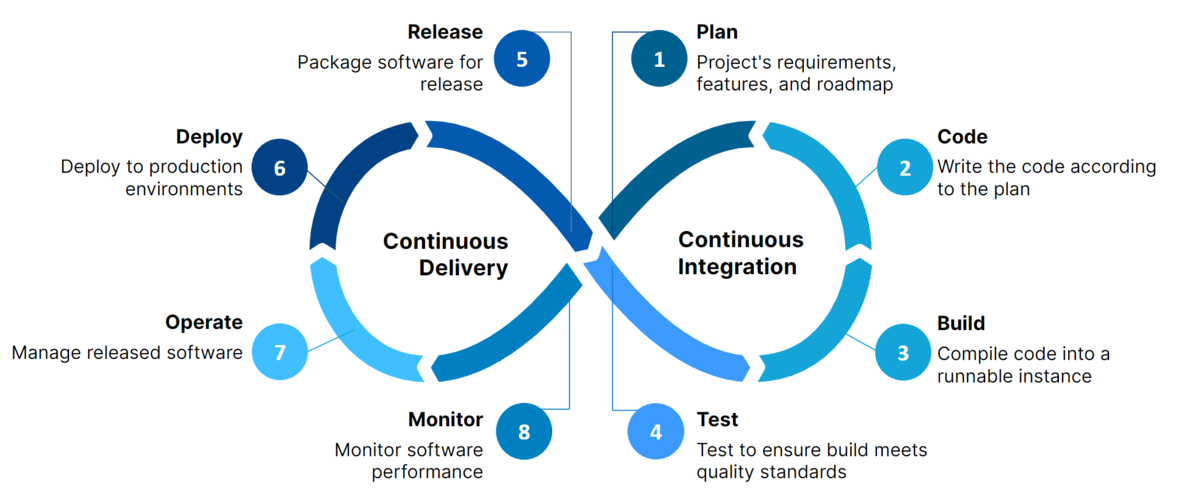
Comprehensive guide to building secure and hardened CI/CD pipelines using GitHub Actions and GitLab CI/CD for DevSecOps teams.

Hands-on guide for engineers to implement secure GitHub organizational access & secrets management at scale.
A comprehensive beginner-friendly guide to the most important threat modeling frameworks in cybersecurity.

Learn Terraform from scratch with this beginner-friendly guide. Step through setup, key concepts, and practical examples—plus grab the ultimate command...
A focused guide on securing Terraform infrastructure-as-code, covering state file protection, least privilege, secrets management, and guardrail automation
A practical reference for essential Linux commands every developer, sysadmin, or security engineer should know—organized for speed, efficiency, and daily...

A breakdown of the rising crypto investment scams known as 'Pig Butchering' how they work, red flags to watch for,...