Drift No More: Automating CICD Security Audits of Configuration Drift
Practical guide for security engineers to automate auditing scripts that detect and remediate configuration drift in cloud and on-prem environments....
by Dan.C
Terraform is a powerful IaC (Infrastructure as Code) tool, but misconfigurations and insecure practices can open doors to serious security breaches. From leaked credentials to over-permissive IAM roles, poor Terraform hygiene is often the root cause of cloud compromise.
This post highlights the key security best practices that I’ve implemented in real-world environments to harden Terraform usage and minimize risk.
Avoid using AdministratorAccess for your Terraform automation or local development.
TerraformDevRole, TerraformProdRole).Tooling Tip:
Use terraform-aws-iam-policy-documents to generate principle-of-least-privilege policies easily.
Terraform’s tfstate contains sensitive information such as:
Best practices:
*.tfstate* to .gitignore and never push to VCS.Automate security scanning of Terraform code before any deployment:
checkov -d .
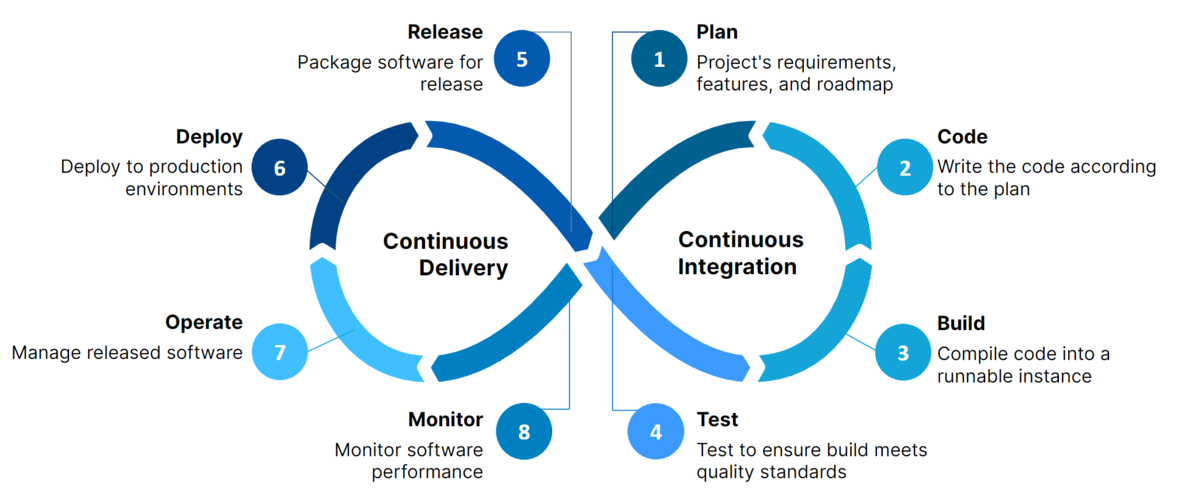
Integrate these into your CI/CD pipeline and fail builds on high-severity findings.
Avoid deploying different environments into the same workspace or backend.
dev, staging, and prod.prod-db, dev-vpc.Hardcoded secrets can easily leak into version control.
Instead, use:
TF_VAR_)Keep modules modular, secure, and testable:
type, regex, etc.)mainEvery terraform apply should go through:
terraform plan reviewSecurity in Terraform isn’t optional — it’s foundational. Secure state, validated inputs, and least privilege access go a long way toward building safe and scalable infrastructure.
Want more? I’ll soon publish a secure AWS Terraform project template with built-in guardrails and automation.
Practical guide for security engineers to automate auditing scripts that detect and remediate configuration drift in cloud and on-prem environments....

Comprehensive guide to understanding, securing, and hardening AI/ML pipelines in both open-source and cloud environments for security engineers.
Comprehensive guide to building secure and hardened CI/CD pipelines using GitHub Actions and GitLab CI/CD for DevSecOps teams.

Hands-on guide for engineers to implement secure GitHub organizational access & secrets management at scale.

Learn Terraform from scratch with this beginner-friendly guide. Step through setup, key concepts, and practical examples—plus grab the ultimate command...
Stay sharp, stay secure. — Dan.C
tags: terraform - iac - devsecops - cloud-security - aws - infrastructure-as-code