Drift No More: Automating CICD Security Audits of Configuration Drift
Practical guide for security engineers to automate auditing scripts that detect and remediate configuration drift in cloud and on-prem environments....
by Dan.C
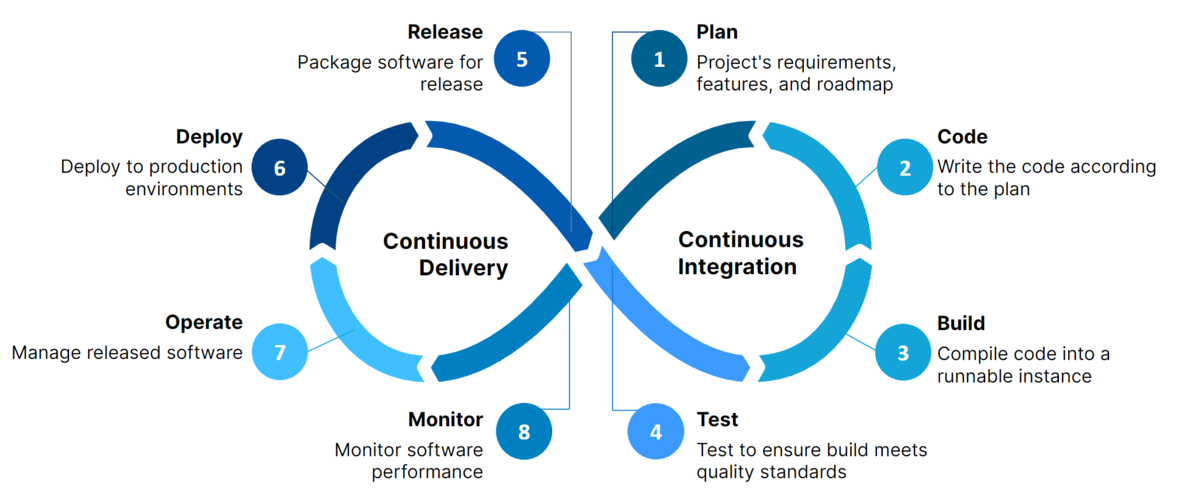
CI/CD (Continuous Integration / Continuous Deployment) pipelines are the backbone of modern software delivery. They allow teams to build, test, and deploy code automatically, increasing efficiency and reducing errors.
However, pipelines are also high-value attack vectors. If compromised, attackers can:
This guide provides practical, step-by-step instructions for security engineers to secure CI/CD pipelines using GitHub Actions and GitLab CI/CD, from general best practices to platform-specific hardening.
CI/CD is a set of practices that automate software delivery:
Benefits:
Risks if misconfigured:
Before diving into hardening pipelines, let’s compare two primary CI/CD platforms:
.github/workflows/..gitlab-ci.yml.Both platforms allow automation of builds, tests, and deployments, but security configurations and best practices differ slightly. We will cover platform-specific guidance below.
Implement these step-by-step to harden pipelines from scratch:
Implementing this checklist before diving into platform-specific hardening ensures a strong baseline.
GitHub Actions allows automation directly in GitHub, with workflows defined in .github/workflows/.
name: CI Pipeline
on:
push:
branches: [main]
pull_request:
branches: [main]
jobs:
build:
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Install dependencies
run: npm ci
- name: Run tests
run: npm test
Explanation:
on: defines events triggering the workflow.jobs: are isolated tasks; runs-on: sets the environment.steps: can run shell commands or call reusable actions.Never store secrets in code. Use GitHub encrypted secrets:
jobs:
deploy:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Configure AWS credentials
uses: aws-actions/configure-aws-credentials@v4
with:
aws-access-key-id: $
aws-secret-access-key: $
Why:
Key security measures:
Use least privilege tokens
Pin third-party actions
uses: actions/checkout@v4 # pinned SHA to prevent supply chain attacks
Restrict branch access
Enable push protection & secret scanning
Limit workflow permissions
permissions:
contents: read # Only read repo content
id-token: write # Only required if using OIDC
Use ephemeral runners or containers
Configured via .gitlab-ci.yml in repo root.
stages:
- build
- test
- deploy
build:
stage: build
image: node:20
script:
- npm ci
- npm run build
artifacts:
paths:
- dist/
test:
stage: test
image: node:20
script:
- npm test
dependencies:
- build
deploy:
stage: deploy
image: amazon/aws-cli:2.13.3
script:
- aws s3 sync ./dist s3://my-bucket --delete
only:
- main
Explanation:
stages: defines the pipeline order.artifacts: persist outputs between jobs.only: restricts deployment to main branch.GitLab uses CI/CD variables:
deploy:
stage: deploy
script:
- echo "Deploying..."
- aws s3 sync ./dist s3://my-bucket --delete
only:
- main
variables:
AWS_ACCESS_KEY_ID: $AWS_ACCESS_KEY_ID
AWS_SECRET_ACCESS_KEY: $AWS_SECRET_ACCESS_KEY
Best practices:
protected: true to restrict usage to protected branches.Pin Docker images
image: node:20@sha256:<digest>
CI/CD pipelines accelerate software delivery, but speed without security is risky.
By following this guide, security engineers can:
Implementing these practices ensures automation enhances productivity without introducing vulnerabilities.
Practical guide for security engineers to automate auditing scripts that detect and remediate configuration drift in cloud and on-prem environments....

Comprehensive guide to understanding, securing, and hardening AI/ML pipelines in both open-source and cloud environments for security engineers.

Hands-on guide for engineers to implement secure GitHub organizational access & secrets management at scale.
A comprehensive beginner-friendly guide to the most important threat modeling frameworks in cybersecurity.
A focused guide on securing Terraform infrastructure-as-code, covering state file protection, least privilege, secrets management, and guardrail automation
Fast delivery shouldn’t mean fragile security. — Dan.C
tags: ci-cd - github-actions - gitlab-ci - devsecops - security - pipeline-hardening - pipeline-security